Review | Key Takeaways from Seminar: Personal Data Protection and Network Security Measures for Companies in the Greater Bay Area – Legal and IT Considerations
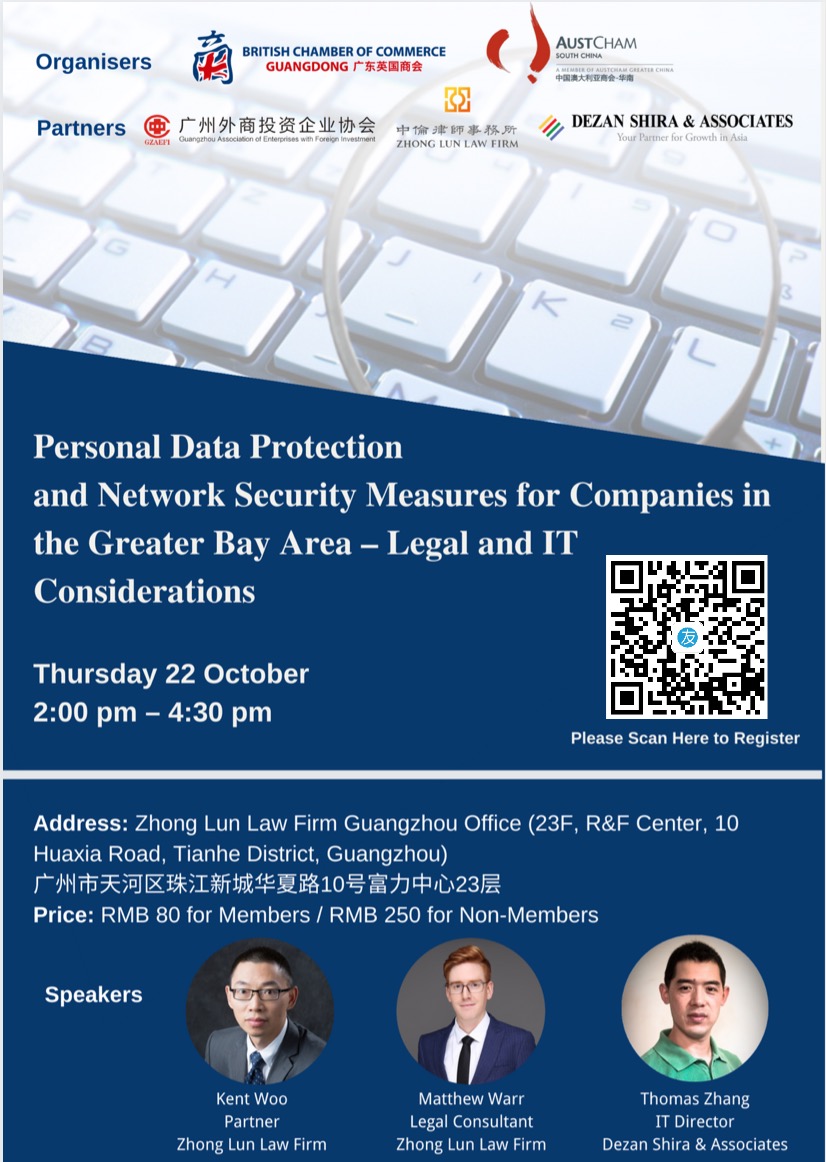
On Thursday 22 October Zhong Lun Law Firm and Dezan Shira & Associates – in collaboration with the British Chamber of Commerce (BritCham) Guangdong, the Australian Chamber of Commerce (AustCham) South China, and the Guangzhou Association of Enterprises with Foreign Investment – organised a seminar at Zhong Lun’s Guangzhou office on personal data protection and network security measures for companies in the Greater Bay Area, from both a legal and IT perspective.
Echo Ji, Events Manager at BritCham Guangdong, began the seminar by introducing and explaining what BritCham Guangdong does, welcoming the participants, and introducing the speakers from Zhong Lun and Dezan Shira & Associates.
Matthew Warr, Legal Consultant at Zhong Lun Guangzhou, then took the stage and started Zhong Lun’s presentation with a story about data leakage that happened in China back in 2016. The story involved a poor high school, university-bound student who, as a result of her personal data being hacked and stolen by a scammer from the computer system of the university at which she was accepted to study, was defrauded for RMB 9,900 and died of a heart attack after learning from the police that it was unlikely that she would recover the money.
Matthew mentioned that when this story happened in 2016, laws in China related to personal data protection were quite rudimentary. However, the story and others like it sparked a national outcry for greater data privacy protections in China, and in the past few years the Chinese government has introduced and implemented a raft of new laws and regulations related to personal data protection and privacy.

Matthew then talked briefly about the differences between the two main models that China considered when drafting its current laws related to data protection – the European Model/GDPR and the US model – and explained that the current trend in China appears to be in favour of the stricter European Model (although the current laws in China are not yet as strict as they are in Europe). He then covered some basics about Chinese laws related to data protection, introducing two important laws recently issued: (1) the Cyber Security Law, which came into force on 1 June 2017, and (2) the Civil Code, which was issued on 28 May 2020 and will come into force next year on 1 January 2021. He also introduced a legal definition of personal information.
Additionally, Matthew covered the legal obligations of companies that collect and use personal information/data (e.g., obtaining consent, informing data subject and relevant authorities if data is divulged, falsified or lost), the rights of individuals with regard to how their data is collected and used (e.g., right to access data or copies of data, right to deletion of data) and the legal restrictions on companies in relation to electronic marketing to individuals (e.g., the importance of obtaining consent of parties concerned before sending advertisements or commercial information).

Following Matthew’s part of Zhong Lun’s presentation, Kent Woo, Partner at Zhong Lun Guangzhou, continued the presentation by introducing some important internal company polices that companies should consider forming and implementing, including a privacy policy, a data protection compliance policy, a data leakage policy, and an employee privacy and monitoring policy. Kent went into specific detail about a company’s privacy policy by talking about why it’s important, the top concerns of authorities in their assessment of a company’s privacy policy, best practice when constructing a privacy policy, and what a privacy policy should include. He also talked in detail about a company’s employee privacy and monitoring policy, explaining, for example, that informed, written and signed consent of employees is required if the employer is monitoring the employees’ work activities/behavior (e.g., if they are collecting/using their personal information from their work computer and email).

Following on from this, Kent covered what to do when data breaches occur (e.g., inform the individual(s) concerned and report to the relevant government authorities) and whether employing Data Protection Officers is required. He then talked about data localisation and cross-border transfers of personal data. Key requirements for transferring data outside China, he explained, include data subject consent and undergoing a security assessment, but that these currently only apply to “Critical Information Infrastructure (CII) Operators”, which are companies operating in certain industries such as energy, transportation, finance, and information services (e.g., TV networks). Kent noted, however, that two measures which are still in draft form expand the abovementioned requirements from CII Operators to all network operators, which basically means all companies that use a network such as the internet. It still remains unclear whether either of the draft measures will take effect in the future.
Kent concluded with the outlook and some developments, noting among other things that a Draft Personal Information Protection Law is expected to be issued for public comment soon and that there have been recent campaigns and increased enforcement by the authorities in relation to personal information protection breaches by APP operators.

Following Zhong Lun’s presentation, Thomas Zhang, Group IT Director at Dezan Shira & Associates, took to the stage to talk about personal data protection and network security measures from an IT perspective.
Thomas started his presentation by introducing several important basic concepts and terminologies about personal data protection as the basis for later introducing technical and organization control measures for personal data protection. These include the definition of identity of personal information from an IT perspective, which is “a kind of link between a piece of information and the individual”, and the different levels of the link (identified individual, pseudonym, and anonymity) which all relate to different technical control measures. Thomas also talked about the different types of personal data based on collection source and sensitivity, and introduced examples of “sensitive” personal information under both China’s Cyber Security Law and Europe’s GDPR. After that, he introduced the relationship between privacy and information security to distinguish their different focuses.
 Following on from this, Thomas introduced the technical control measures for personal data protection. He started from the analysis of the traditional security architecture and its weakness when facing different modern security threats, then introduced the modern security model, “Zero Trust Security Architecture”, which “never trusts, always verifies” each access request on resource on a very low granularity level.
Following on from this, Thomas introduced the technical control measures for personal data protection. He started from the analysis of the traditional security architecture and its weakness when facing different modern security threats, then introduced the modern security model, “Zero Trust Security Architecture”, which “never trusts, always verifies” each access request on resource on a very low granularity level.
Later, Thomas introduced several common and widely used technical control measures for personal data protection, which include: 1) encryption (which can be implemented based on different data states: Data at Rest, Data in Motion, Data in Use); 2) DLP/IRM (Data Loss Prevention can be mainly used for data leakage from organization to external party, while Information Right Management provides continuous protection, even for the data being shared with external parties already); 3) IAM (Identity and Access Management is an important and effective tool for data access control and user management, while anti-phishing training and implementation of Multi-Factor Authentication are two important ways for account protection); 4) De-identification (which is used to remove or reduce the correlation between info and specific individual, and accordingly reduce the risk to personal data). Privacy be Default and Privacy by Design (PbD) was introduced last in this section and Thomas explained the advantages and importance of PbD and how to perform it from both Identifiability and Centricity dimensions.
In addition to the technical control measures, Thomas also introduced some organization control measures for personal data protection. He first introduced software ecosystem for privacy and a suggested organization structure for privacy management, and then talked about some industry standards like China’s “Personal Information Security Specification” and ISO 27001 / 27701 / 27018. Following that, Thomas explained the necessity of Data Protection Impact Assessment (DPIA), its objective and output, and the detailed steps to conduct DPIA with emphasis on Data Mapping when describing the Information Flows. Lastly, Thomas introduced the Data Protection & Privacy Management System (DPMS) and 5 steps (Preparation, Organization, Implementation, Governance, and Evaluation) to develop and maintain DPMS.
 In the final part of his presentation, Thomas introduced the personal data life cycle, from Collection, Processing, Storage, Distribution to Destruction, then summarized the technical and organizational control measures which can be used to cover different stages of data life cycle. Lastly, Thomas emphasized the seven most fundamental principles on Privacy, which were originally introduced by Ann Cavoukian, the former Information and Privacy Commissioner for the Canadian province of Ontario. The seven principles are as follows:
In the final part of his presentation, Thomas introduced the personal data life cycle, from Collection, Processing, Storage, Distribution to Destruction, then summarized the technical and organizational control measures which can be used to cover different stages of data life cycle. Lastly, Thomas emphasized the seven most fundamental principles on Privacy, which were originally introduced by Ann Cavoukian, the former Information and Privacy Commissioner for the Canadian province of Ontario. The seven principles are as follows:
1) Proactive, not Reactive; Preventative, not Remedial;
2) Privacy as the Default Setting;
3) Privacy embedded into Design;
4) Full functionality: Positive Sum, not Zero Sum;
5) End-to-End Security: Protection in while Life Cycle;
6) Visibility and Transparency: Keep it Open;
7) Respect user’s Privacy: Keep it user-centric.
Thomas explained and shared his insights on each of the above principles.
BritCham Guangdong, AustCham South China and the Guangzhou Association of Enterprises with Foreign Investment really appreciated the time and effort that was put in by Matthew Warr and Kent Woo of Zhong Lun, and Thomas Zhang of Dezan Shira & Associates. It was a valuable and informative session.
We received lots of positive feedback and are looking to holding similar informative seminars in the future and continuing to bring value to our members and the wider community.
If you have any further questions about the presentation by Zhong Lun Law Firm, feel free to reach out to Matthew Warr at matthewwarr@zhonglun.com
If you have any further questions about the presentation by Dezan Shira & Associates, feel free to reach out to Thomas Zhang at thomas.zhang@dezshira.com
关于中国-澳大利亚华南商会-华南
The China – Australia Chamber of Commerce – South China (AustCham South China) was established in1994 to develop, promote and expand business relations between Australia and China through the representation of its membership.
As a registered NGO office in the People’s Republic of China, AustCham South China serves as Australia’s peak industry advocacy body in South China and supports its members by providing information, connections, business services and government relations assistance.